I am constantly looking for students (
English |
Chinese
). If you're passionate about computer security, please consider joining my group and build something exciting!
GMU ranks 32rd overall (13th in Security) on
CSRankings.
About GMU and Why Join Us
|
Research Areas & Interests
|
My research interests lie in hardware and system security, with a particular focus on the following areas:
• AR/VR Security and Privacy
- Software-based side-channel attacks on AR/VR [Security’23a]
- Inferring VR keystrokes via user head motion [Security’23b]
- Shared-state attacks in multi-user AR [Security’24]
- Acoustic attacks on IMU sensors in XR headsets [ISMAR’25]
- Exploring vulnerabilities of LLM-integrated XR systems [arXiv’25]
• Microarchitectural / System Security
- Stealing DNN models via GPU context-switching side channels [DSN’20]
- Model extraction using remote FPGA power side channels [TIFS'21]
- Microarchitectural attacks on NVLink [SEED'24] [CCS'26]
- Exploiting GPU memory via Rowhammer mitigation techniques (RFM) [Security’25]
- Attacking Linux/Android file systems via
syncfs [S&P’25]
- GPU kernel validation via composable side channel signals [arXiv’25]

|
Recent News
|
|
– May 2026 [Paper]: NVBleed has been accepted to ACM CCS 2026! See you in Netherlands!
– May 2026 [Service]: I am invited to serve on the program committee of HPCA 2027.
– April 2026 [Funding]: I received grant from Commonwealth Cyber Initiative (CCI) with Khaled Khasawneh. Thank you for supporting our research!
– April 2026 [Service]: I am invited to serve on the program committee of ImmerCom 2026, and XR Security 2026.
– March 2026 [Service]: I am invited to serve on the program committee of ASIACCS 2027, and ASPLOS 2027.
– February 2026 [Service]: I am invited to serve on the program committee of MICRO 2026, and NEHWS 2026.
– January 2026 [People]: Welcoming Zixun and Hao to the lab!
– November 2025 [Activity]: I successfully defended my PhD. I am now Dr. Zhang!
– October 2025 [Activity]: I was invited to give a talk with Jiasi Chen at the First Workshop on Enhancing Security, Privacy, and Trust in Extended Reality (XR) Systems (XR Security 2025)!
– September 2025 [Award]: I was awarded the UCR Dissertation Completion Fellowship to support my final quarter at UCR.
– July 2025 [Paper]: Our paper on attacking AR/VR headsets' IMU sensors via acoustic signals has been accepted to IEEE ISMAR 2025! Shout out to Zijian!
– July 2025 [Service]: I will be serving on the Program Committee for HOST 2026. Please consider submitting your work!
– July 2025 [Service]: I will be serving on the Program Committee for two AR/VR workshops: VARSE 2025 (co-located with ASE 2025) and XR Seucrity 2025 (co-located with MobiHoc 2025). Please consider submitting your work!
– June 2025 [Activity]: I will join George Mason University as an Assistant Professor starting next January! I am actively recruiting Ph.D. students to join my research group.
– March 2025 [Paper]: My Ph.D. dissertation has been accepted to the HOST 2025 Ph.D. Dissertation Competition! See you in San Jose!
– March 2025 [Paper]: Our paper on attacking Linux/Android file systems via syncfs has been accepted to IEEE S&P 2025! Shout out to Cheng—he will be joining the University of Rochester as a Ph.D. student. Congrats!
– January 2025 [Paper]: Our paper on attacking GPUs via Rowhammer RFM mitigation has been accepted to USENIX Security 2025! Shout out to Ravan!
– September 2024 [Paper]: We wrote a blog post on microarchitecture security research at USENIX Security 2024.
– August 2024 [Activity]: I passed my oral qualifying examination and became a Ph.D. candidate!
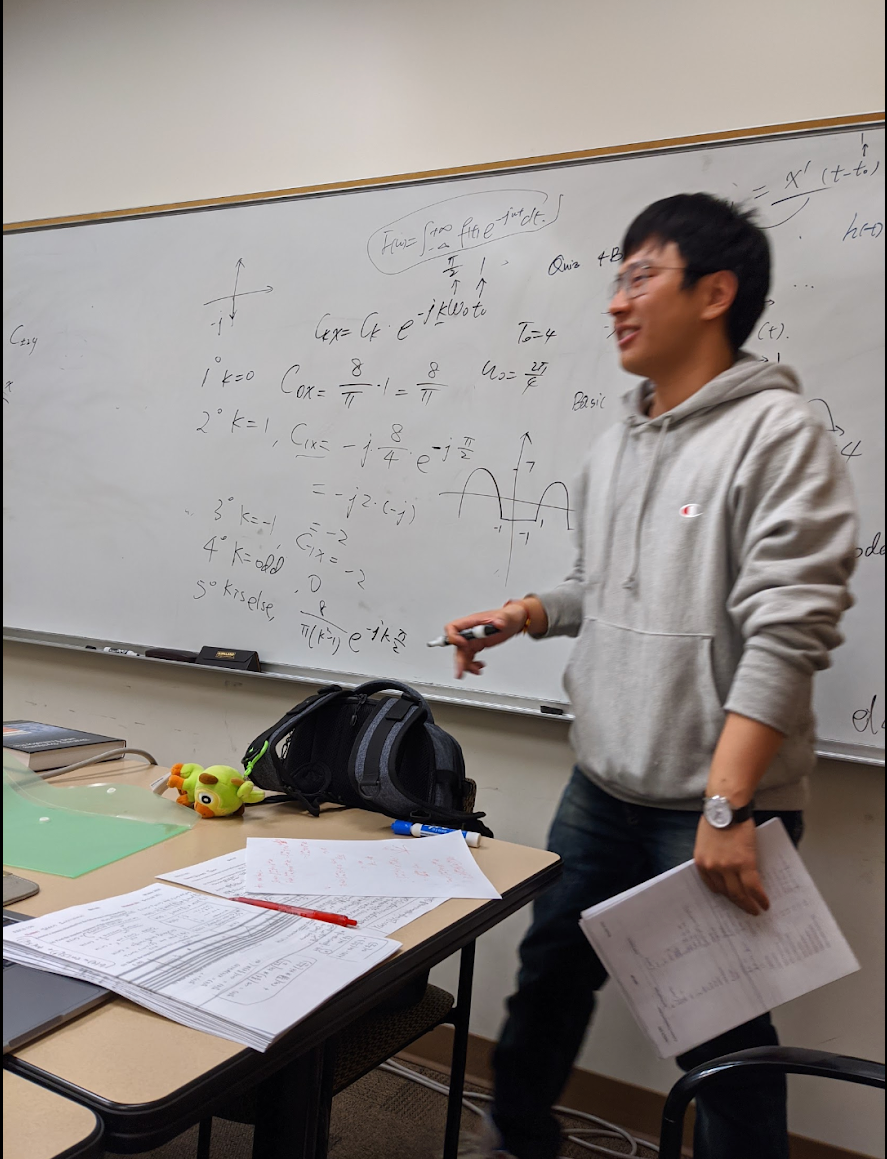
– June 2024 [Teaching]: I taught an upper-division undergraduate course this summer (syllabus).
– May 2024 [Paper]: I presented our work Beyond the Bridge at SEED 2024 in Orlando.
– April 2024 [Service]: I served as a volunteer organizing ASPLOS 2024. Amazing experience!
– February 2024 [Paper]: Our multi-user AR security paper was accepted to USENIX Security 2024. See you in Philly!
– December 2023 [Paper]: One short paper accepted to IEEE SEED 2024. See you in Orlando!
– November 2023 [Paper]: I presented our work at the SC 2023 Workshop in Denver.
– September 2023 [Paper]: One paper accepted to the SC 2023 Workshop.
– September 2023 [Activity]: I completed my internship at PNNL.
– August 2023 [Paper]: I presented It’s All in Your Head(set) at USENIX Security 2023 in Anaheim.
– August 2023 [Media]: Our AR/VR security research was featured in the news [UCR News] [ZME Science].
– March 2023 [Activity]: I joined PNNL as a Ph.D. intern for Summer 2023.
– February 2023 [Paper]: Our work on AR/VR security was accepted to USENIX Security 2023.
– November 2022 [Paper]: One AR/VR security paper accepted to USENIX Security 2023. My first Big 4 security paper!
– May 2022 [Activity]: Received a student travel grant from the gem5 Bootcamp 2022.
– July 2021 [Activity]: Received a student travel grant from USENIX Security 2021.
– July 2021 [Paper]: One paper accepted to IEEE TIFS.
– May 2021 [Activity]: Received a student travel grant from IEEE S&P 2021.
– February 2021 [Paper]: One poster accepted to FPGA 2021.
– June 2020 [Paper]: One paper accepted to DSN 2020.
|

|
Publications
|
-
Students advised: marked with #. Co-first authors: marked with *.
-
Selected papers are
highlighted.
|
| CCS 2026 |
NVBleed: Covert and Side-Channel Attacks on NVIDIA Multi-GPU Interconnect
Yicheng Zhang,
Ravan Nazaraliyev,
Sankha Baran Dutta,
Andres Marquez,
Kevin J. Barker,
Nael Abu-Ghazaleh
The 33rd ACM Conference on Computer and Communications Security (CCS), Hague, Netherlands, November, 2026.
PDF
/
BibTex
|
|
| arXiv 2025 |
Evil Vizier: Vulnerabilities of LLM-Integrated XR Systems
Yicheng Zhang*,
Zijian Huang*,
Sophie Chen,
Erfan Shayegani,
Jiasi Chen,
Nael Abu-Ghazaleh
PDF
/
BibTex
|
|
| arXiv 2025 |
ShadowScope: GPU Monitoring and Validation via Composable Side Channel Signals
Ghadeer Almusaddar*,
Yicheng Zhang*,
Saber Ganjisaffar,
Barry Williams,
Yu David Liu,
Dmitry Ponomarev,
Nael Abu-Ghazaleh
PDF
/
BibTex
|
|
| ISMAR 2025 |
Siren Song: Acoustic Attacks on Pose Estimation in XR Headsets
Zijian Huang,
Yicheng Zhang,
Sophie Chen,
Nael Abu-Ghazaleh,
Jiasi Chen
The 24th IEEE International Symposium on Mixed and Augmented Reality, Daejeon, South Korea, October, 2025.
Acceptance Rate: 21.1% (161/762)
PDF
/
Blog (In Chinese)
/
Slides
/
BibTex
|
|
| USENIX Sec 2025 |
Not so Refreshing: Attacking GPUs using RFM Rowhammer Mitigation
Ravan Nazaraliyev,
Yicheng Zhang,
Sankha Baran Dutta,
Andres Marquez,
Kevin J. Barker,
Nael Abu-Ghazaleh
The 34th USENIX Security Symposium, Seattle, WA, USA, August, 2025.
Acceptance Rate: 17.1% (407/2385)
PDF
/
Code
/
BibTex
Badges: Available, Functional
|
|
| IEEE S&P 2025 |
I Know What You Sync: Covert and Side Channel Attacks on File Systems via syncfs
Cheng Gu#,
Yicheng Zhang,
Nael Abu-Ghazaleh
The 46th IEEE Symposium on Security and Privacy, San Francisco, CA, USA, May, 2025.
Acceptance Rate: 14.8% (257/1740)
PDF
/
Slides
/
BibTex
|
|
| SafeAR 2024 |
Securing Shared State in Multi-User Augmented Reality
Jiasi Chen,
Carter Slocum,
Yicheng Zhang,
Erfan Shayegani,
Pedram Zaree,
Nael Abu-Ghazaleh
2024 IEEE International Symposium on Mixed and Augmented Reality Adjunct (ISMAR-Adjunct), Seattle, WA, USA, October, 2024.
PDF
/
BibTex
|
|
| USENIX Sec 2024 |
That Doesn't Go There: Attacks on Shared State in Multi-User Augmented Reality Applications
Carter Slocum*,
Yicheng Zhang*,
Erfan Shayegani,
Pedram Zaree,
Nael Abu-Ghazaleh,
Jiasi Chen
The 33rd USENIX Security Symposium, Philadelphia, PA, USA, August, 2024.
Acceptance Rate: 18.3% (417/2276)
PDF
/
Slides
/
Video
/
Website
/
Blog (In Chinese)
/
BibTex
|
|
| IEEE SEED 2024 |
Beyond the Bridge: Contention-Based Covert and Side Channel Attacks on Multi-GPU Interconnect
Yicheng Zhang,
Ravan Nazaraliyev,
Sankha Baran Dutta,
Nael Abu-Ghazaleh,
Andres Marquez,
Kevin J. Barker
2024 IEEE International Symposium on Secure and Private Execution Environment Design, Orlando, FL, USA, May, 2024.
PDF
/
Slides
/
BibTex
|
|
| SC Workshop 2023 |
Accuracy-Constrained Efficiency Optimization and GPU Profiling of CNN Inference for Detecting Drainage Crossing Locations
Yicheng Zhang,
Dhroov Pandey,
Di Wu,
Turja Kundu,
Ruopu Li,
Tong Shu
SC'23 Workshops of The International Conference on High Performance Computing, Network, Storage, and Analysis, Denver, CO, USA, November, 2023.
PDF
/
Slides
/
BibTex
|
|
| USENIX Sec 2023 |
Going through the motions: AR/VR keylogging from user head motions
Carter Slocum,
Yicheng Zhang,
Nael Abu-Ghazaleh,
Jiasi Chen
The 32nd USENIX Security Symposium, Anaheim, CA, USA, August, 2023.
Acceptance Rate: 29.2% (422/1444)
PDF
/
Slides
/
BibTex
/
Blog (In Chinese)
*Media Coverage*:
[UCR News]
[Game Is Hard]
[Gillett News]
[Tech Xplore]
|
|
| USENIX Sec 2023 |
It's all in your head(set): Side-channel attacks on AR/VR systems
Yicheng Zhang,
Carter Slocum,
Jiasi Chen,
Nael Abu-Ghazaleh
The 32nd USENIX Security Symposium, Anaheim, CA, USA, August, 2023.
Acceptance Rate: 29.2% (422/1444)
PDF
/
Slides
/
BibTex
/
Blog (In Chinese)
*Media Coverage*:
[UCR News]
[ZME Science]
[Fagen Wasanni]
[Analytics Insight]
|
|
| IEEE TIFS 2021 |
Stealing Neural Network Structure through Remote FPGA Side-channel Analysis
Yicheng Zhang,
Rozhin Yasaei,
Hao Chen,
Zhou Li,
Mohammad Abdullah Al Faruque
IEEE Transactions on Information Forensics and Security, August, 2021.
PDF
/
Slides
/
BibTex
|
|
| FPGA 2021 |
Poster: Stealing Neural Network Structure through Remote FPGA Side-channel Analysis
Yicheng Zhang,
Rozhin Yasaei,
Hao Chen,
Zhou Li,
Mohammad Abdullah Al Faruque
The 2021 ACM/SIGDA International Symposium on Field-Programmable Gate Arrays, Virtual Event USA, February, 2021.
Abstract
/
BibTex
|
|
| DSN 2020 |
Leaky DNN: Stealing Deep-Learning Model Secret with GPU Context-Switching Side-Channel
Junyi Wei*,
Yicheng Zhang*,
Zhe Zhou,
Zhou Li,
Mohammad Abdullah Al Faruque
The 50th IEEE/IFIP International Conference on Dependable Systems and Networks (DSN), Valencia, Spain, June, 2020.
Acceptance Rate: 16.5% (48/291)
PDF
/
Slides
/
Video
/
Code
/
BibTex
|

|
Current Group Members
|
I lead the MASS Lab (Mason Augmented/Virtual Reality and System Security Lab), and work with the following talented students:

|
Teaching
|
 |
At GMU, I teach the following courses:
FPGA Design with VHDL
(Syllabus)
Instructor for ECE 448 – Spring 2026
|
 |
At UC Riverside, I was the lead instructor for an upper-division undergraduate course in Summer 2024.
Design of Operating Systems
(Syllabus)
Associate Instructor for CS 153 – Summer 2024
|
|
Professional Service (Selected)
|

|
Honors and Awards
|
|
UCR Dissertation Completion Fellowship | UC Riverside
|
2025
|
|
International Peer Educator Training Program Certification | CRLA
|
2023
|
|
Conference Travel Grant | UCR GSA
|
2023
|
|
Student Travel Grant | 1st gem5 Boot Camp
|
2022
|
|
Student Travel Grant | 30th USENIX Security Symposium
|
2021
|
|
Student Travel Grant | 42nd IEEE Symposium on Security and Privacy
|
2021
|
|
Dean's Distinguished Fellowship Award | UC Riverside
|
2021
|

|
About me
|
 |
In my free time, I love to play Dota 2 with my friends. I have played this game for over 6k hours (over 2% of my lifetime) ╚(″⚈ᴗ⚈)╗
In 2023, I went to Seattle to watch Ti12 with my wife and 4-month-old son.
I always support CN Dota (Chinese Dota 2), no matter how many times we lose.
历尽千帆,剑心犹在
|
|